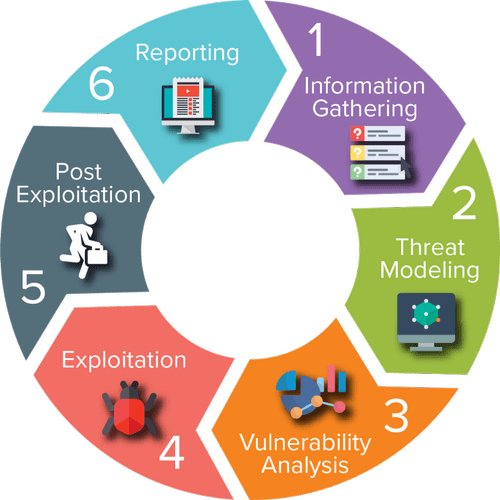
Ethical hacking is the practice of attempting to infiltrate and exploit a system in order to find out its weaknesses and better secure it.
I segment the field of ethical hacking into two primary components:
penetration testing for a legitimate information security firm and working
for your nation’s military or intelligence agencies.

Penetration Testing
As organizations become increasingly security conscious and the cost of
security breaches rise exponentially, many large organizations are beginning
to contract out security services. One of these key security services is
Penetration Testing
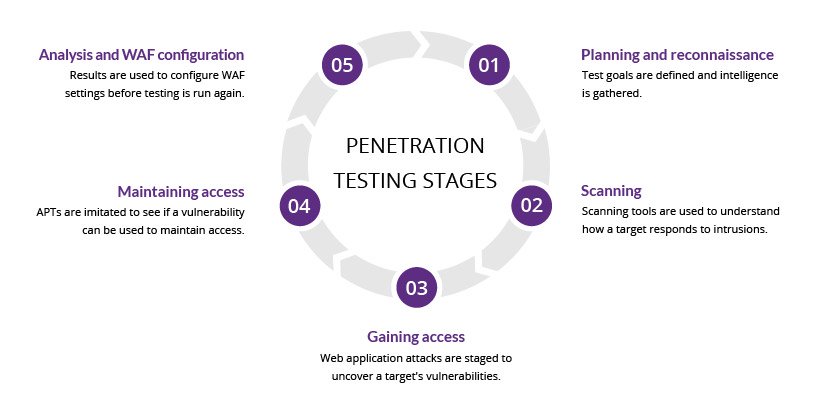
A penetration test is essentially a legal, commissioned
hack to demonstrate the vulnerability of a firm’s network and systems.
Generally, organizations conduct a vulnerability assessment first to find
potential vulnerabilities in their network, operating systems, and services.
I emphasize potential, as this vulnerability scan includes a significant number of
false positives (things identified as vulnerabilities that really are not). It is the
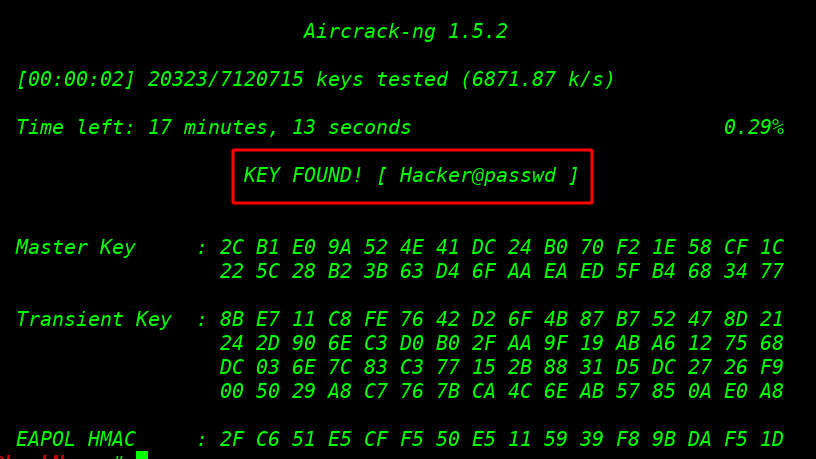
role of the penetration tester to attempt to hack, or penetrate, these
vulnerabilities.