In this post, we are going to solve another Vunhub machine called Who Want To Be King. This another boot-2-root challenge from vulnhub, you can download here the Machine.
Network Scanning
Let’s find the target VM IP address run the netdiscover command.
|
1 |
sudo netdiscover |
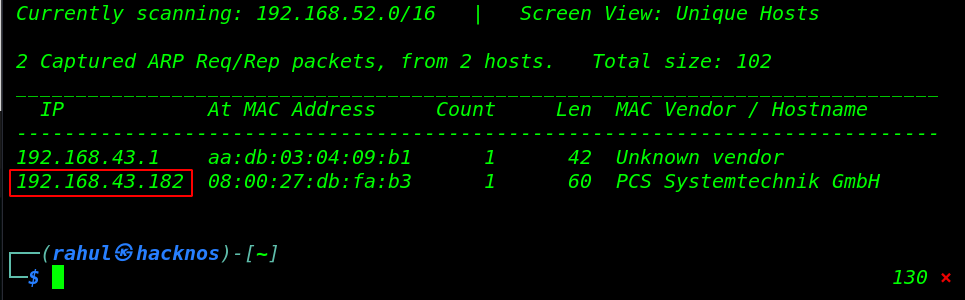
Now we have an IP address target machine, In my case, my target IP address is (192.168.4.182. and our next step is scanning the target machine’s IP address and finding open ports and running service using the nmap command.
|
1 |
nmap -sV -sC 192.168.43.182 |
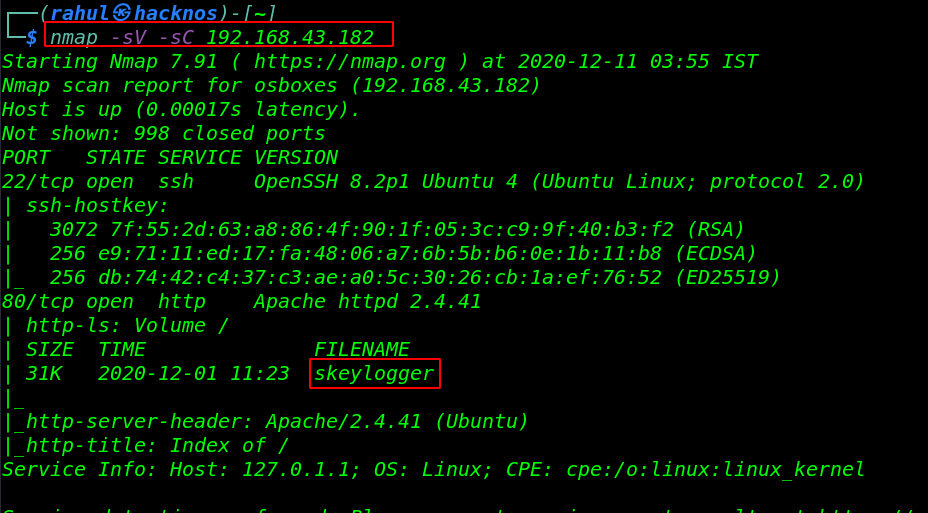
The Nmap scanning output shows us that there are 2 ports open: 22/SSH, 80/HTTP apache httpd server running.
Enumeration
Since We find that port 80 is open and running apache httpd server, so we open the target IP in our browser.
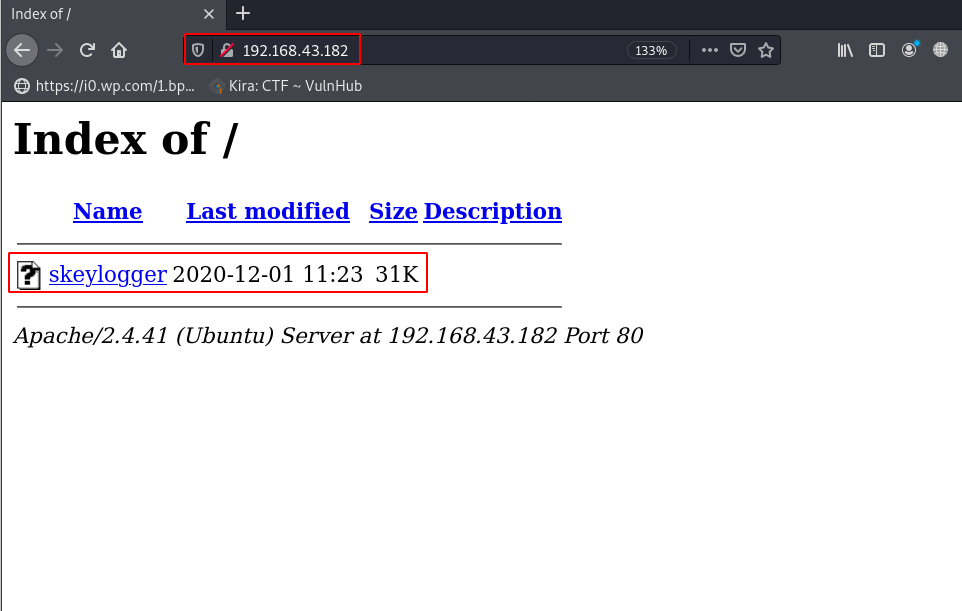
After navigating the target machine IP we found a skeylogger binary file, we download the skeylogger on our local machine. then we try to enumerate useful information in the skeylogger file using the strings tool.
|
1 |
strings skeylogger |
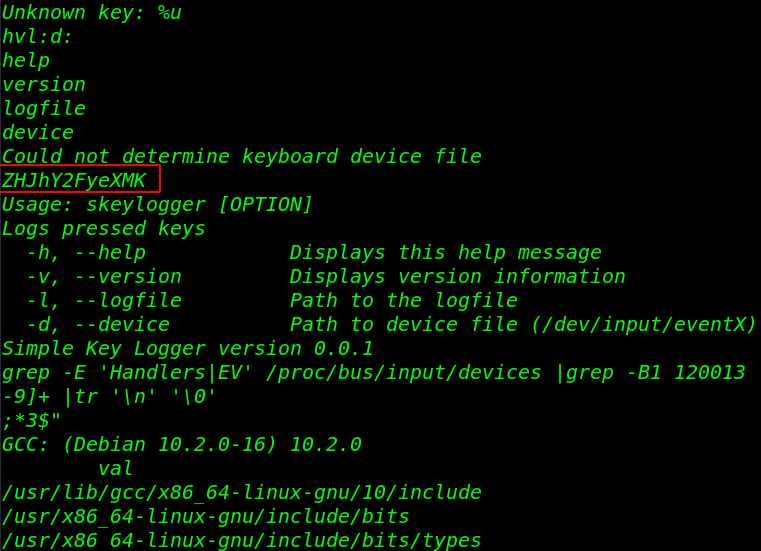
and we got a useful base64 encoded string, let’s decode it.
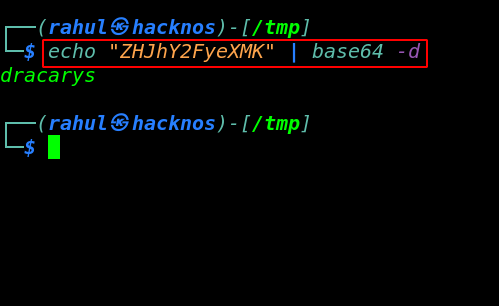
After decoding the base64 encoded string we get a text ( dracarys ), we searched on Google What is dracarys in got and get much more information about the dracarys text.
Let’s try to login with the SSH server using daenerys username and password dracarys, and we successfully login with SSH Server.
|
1 |
ssh deanerys@192.168.43.182 |
Now we have a shell access target machine, we start enumerating the directories and files and we found a zip compress file daenerys.zip, using the unzip command to extract the zip file.
|
1 2 3 4 5 6 |
ls cat secret cd .local/share/ ls unzip daenerys.zip cat djkdsnkjdsn |
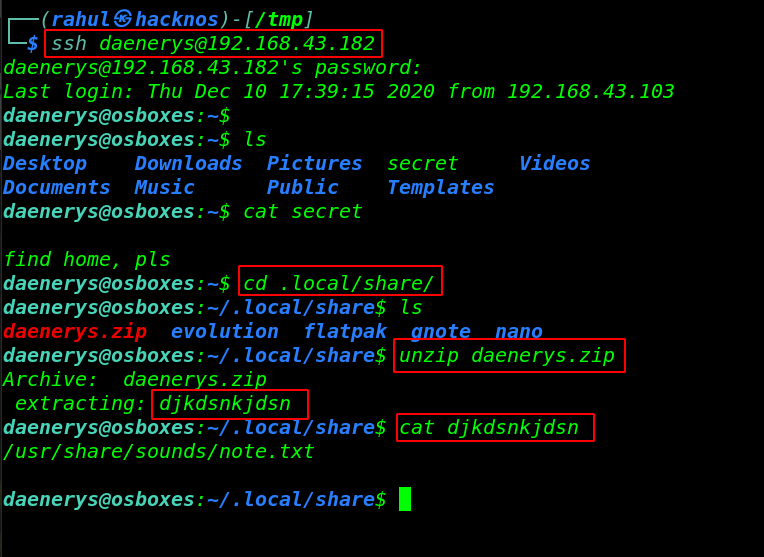
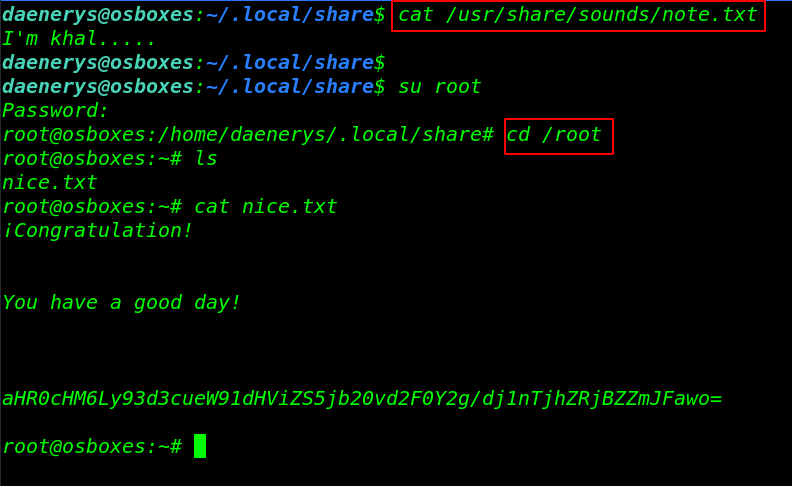
We get another hint in the djkdsnkjdsn file, let’s read the note.txt files using the cat command and again get a message I’m Khal again we searched on google for I’m Khal and the output give use full name khaldrogo.
again we try to switch the user Daenerys to root using the khaldrogo password, and we successfully change our user, now we have root shell access let’s move the /root directory and read the last root flag.
|
1 2 3 4 |
cat /usr/share/sounds/note.txt su root cd /root cat nice.txt |